How to Secure OT and Plant Operations Without Causing Downtime
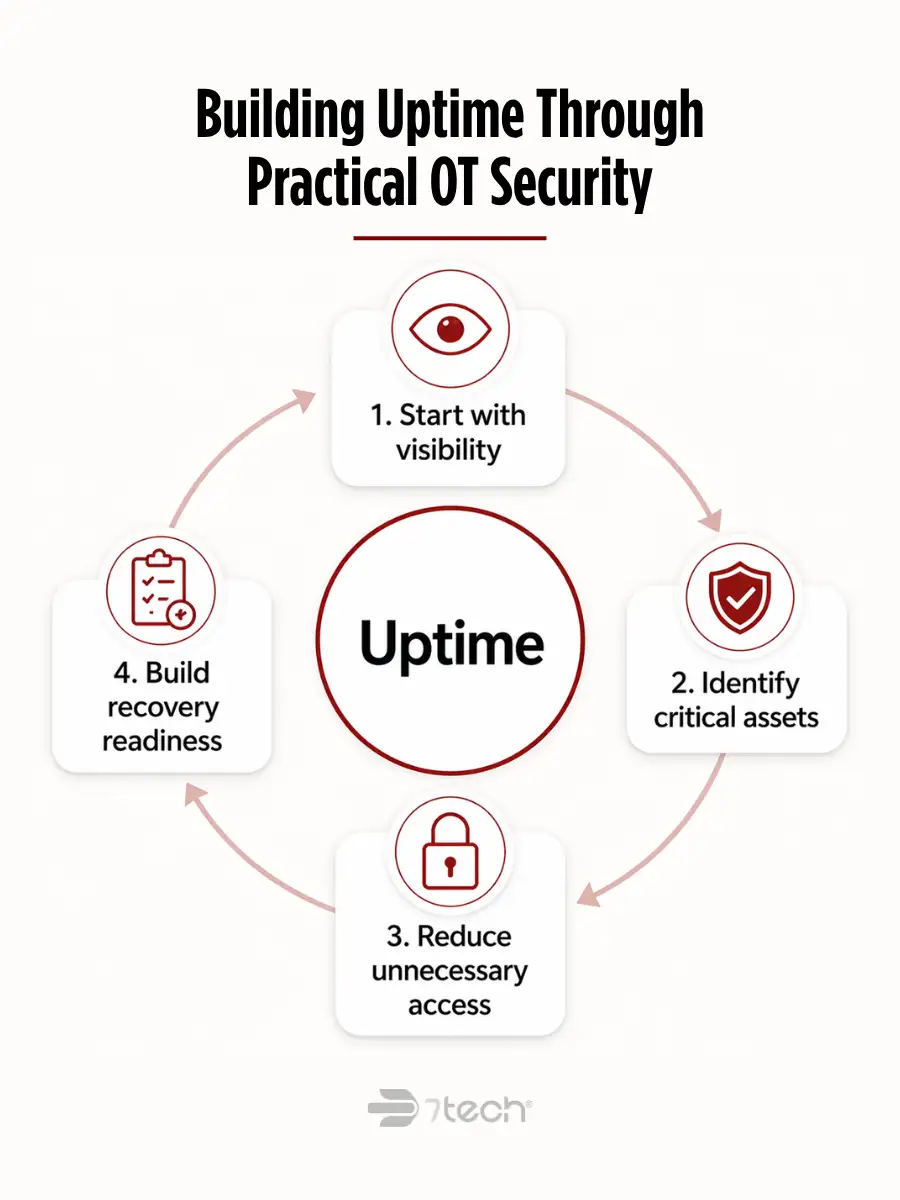
To secure OT and plant operations without creating new downtime, manufacturers need a phased approach that starts with visibility, prioritizes the systems that matter most to production, limits unnecessary access, and builds recovery readiness before an incident forces decisions under pressure. The goal is not just better cybersecurity. It is stronger uptime, safer operations, and more defensible business continuity.
For executive leaders, OT security is as much an operations issue as a technology issue. If a plant network is compromised, the result is not just an IT problem. It can affect output, safety, vendor coordination, customer commitments, and leadership credibility.
That is why OT security has to be planned differently from ordinary office IT controls. The objective is to reduce cyber risk while respecting production realities, maintenance windows, and the fact that many plant environments were never designed for frequent change. Manufacturing-focused public guidance such as the CISA critical manufacturing security guide reinforces that plant security has to be approached in the context of operational resilience, not just technical control coverage.
What It Means to Secure OT and Plant Operations
Operational technology, or OT, includes the systems and connected devices that help run physical processes in a plant. That can include industrial controllers, HMIs, sensors, supervisory systems, production support networks, and other equipment tied directly to manufacturing operations.
Securing OT and plant operations means protecting the environment that keeps production moving. In practice, that includes:
- Protecting critical production assets from disruption
- Reducing the likelihood of ransomware or unauthorized access affecting plant availability
- Limiting the spread of problems between business IT and plant systems
- Improving visibility into what is connected, who can access it, and what is changing
- Preparing recovery plans that reflect how the plant actually operates
OT security is not the same as traditional business IT security. In office IT, a restart, patch, or device replacement may be inconvenient. In OT, the same action may interrupt production, affect quality, delay shipments, or create safety concerns. That is why OT protection should be grounded in availability, reliability, safety, and operational continuity from the start.
For a useful baseline on how OT differs from enterprise IT, many manufacturers look to NIST OT security guidance, which frames OT protection around safety, availability, and resilience.
Why Manufacturers Struggle to Secure OT Environments
Most manufacturers are not struggling because they are inattentive. They are dealing with real plant-floor constraints.
- Legacy equipment: Many systems were built for long service lives, not modern security expectations.
- Limited asset visibility: It is common to have devices, vendor tools, and unmanaged connections that are poorly documented.
- Production-first culture: Teams are rightly cautious about changes that might interrupt output.
- Vendor sprawl: Integrators, OEMs, contractors, and remote support providers often create overlapping access paths.
- Patching limitations: Some systems cannot be updated on a normal IT cadence without operational risk.
- IT and OT disconnect: Security ownership is often split, while accountability remains unclear.
- Aging systems and fragmented governance: As environments evolve over time, no single leader may have a complete picture.
These conditions make OT security harder, but they also explain why a low-disruption plan matters. Manufacturers rarely need a dramatic overhaul. They need a clear sequence of improvements that lowers risk without creating unnecessary change.
This is also where broader manufacturing security strategies become more practical when they are tied directly to plant uptime, ownership, and recovery planning.
The Biggest Threats to Plant Operations
The most serious OT security threats are the ones that interrupt production or complicate recovery.
- Ransomware: Not just a data event, but a business continuity event that can halt scheduling, plant communications, and production support systems.
- Remote access misuse: Third-party support paths, persistent connections, and weak access controls can create avoidable exposure.
- Lateral movement across flat networks: If business IT and plant environments are too open, one compromise can spread farther than it should.
- Insider or contractor risk: Over-permissioned users and temporary access that never gets removed create operational risk.
- Unmanaged devices: Unknown assets are difficult to monitor, patch, or isolate.
- Poor recovery readiness: Even when the initial incident is contained, downtime can last longer if backups, restoration steps, and escalation paths are unclear.
Guidance such as CISA ICS cybersecurity best practices is useful here because it ties practical controls like segmentation, boundary protection, and access discipline directly to risk reduction in industrial environments. When you need a deeper look at ransomware-specific plant disruption, this resource on how to protect your manufacturing plant from ransomware is a useful companion to a broader OT strategy.
How to Secure OT and Plant Operations: A Practical 6-Step Framework
The safest way to improve OT security is usually the least dramatic one: fix the highest-risk gaps first, stage changes around plant realities, and make every control support continuity rather than compete with it.
1. Identify your critical OT assets and production dependencies
Start with the systems, devices, and processes that matter most to production. Which assets drive throughput? Which ones affect safety, quality, or scheduling? Which failures would create the most expensive or disruptive downtime?
This step is foundational because security priorities should follow operational priorities. Not every device carries the same risk. The goal is to focus first on the systems that support essential plant functions and the dependencies around them.
2. Segment OT from business IT and limit unnecessary access
One of the most practical ways to secure plant operations is to reduce flat-network exposure. OT and business IT do not need the same level of openness. Separating environments where appropriate and limiting access to what operations actually require can reduce the spread of malware, credential misuse, and accidental disruption.
This is not about making the plant harder to run. It is about making sure ordinary business-side issues do not gain an easy path into production systems. Manufacturers looking for broader manufacturing IT services often find segmentation to be one of the highest-value controls when it is planned carefully and implemented in phases.
3. Secure remote vendor and contractor connections
Many manufacturers rely on outside vendors, integrators, and service providers to support equipment and specialized systems. That makes remote access a business reality, but it should not remain broad, persistent, or poorly monitored.
Review who can connect, how they connect, when they connect, and what they can reach. Temporary access is generally safer than standing access. Approval paths, logging, and periodic access reviews also make leadership oversight easier.
4. Improve monitoring, alerting, and visibility
You cannot protect what you cannot see. OT visibility should improve understanding of assets, activity, and abnormal behavior across the plant environment.
Better visibility helps operations leaders, IT leaders, and executives in different ways:
- Operations teams gain more confidence in what is connected and changing
- IT and security teams can coordinate faster when something looks wrong
- Executives gain clearer reporting and fewer surprises
For many organizations, this is where efforts to improve manufacturing cybersecurity start becoming practical rather than abstract, because visibility creates the context needed for better decisions, better escalation, and more accountable response.
5. Build ransomware recovery and continuity plans
Ransomware remains one of the clearest threats to plant continuity, but the executive question is broader than prevention alone: if something does get through, how quickly can the organization contain it, communicate clearly, and restore operations?
Recovery planning should reflect plant realities, not generic office assumptions. That means backup priorities, restoration sequencing, communications, vendor coordination, and manual workarounds should all be aligned to the production environment. Public-sector guidance such as CISA ransomware guidance is useful here because it emphasizes preparedness and recovery, not just defense.
6. Test response processes before an incident happens
Plans look stronger on paper than they do during an actual disruption. That is why testing matters. Manufacturers should clarify ownership, escalation paths, communications, and decision authority before an incident occurs.
Even a focused tabletop exercise can reveal gaps in who approves shutdown decisions, who contacts vendors, who informs leadership, and how the organization decides what comes back first. Good testing reduces confusion, shortens downtime, and improves defensibility after the fact.
How to Strengthen OT Security Without Disrupting Production
The most effective OT security improvements are usually phased, risk-based, and coordinated with maintenance realities.
- Roll changes out in stages: Avoid large, simultaneous changes in sensitive production environments.
- Prioritize by operational risk: Focus first on the gaps that could create the greatest business impact.
- Coordinate with maintenance windows: Security changes should respect uptime requirements and planned downtime schedules.
- Use cross-functional ownership: OT, IT, operations, compliance, and leadership all need a role.
- Measure clarity, not just control count: Better reporting and fewer surprises matter to executive teams.
If the concern is downtime prevention, the right question is not, “How fast can we add controls?” It is, “Which improvements reduce exposure while preserving production stability?” Practical frameworks such as the CISA Cybersecurity Performance Goals support that phased approach by helping organizations prioritize improvements without trying to change everything at once.
That same discipline also supports wider efforts to eliminate IT downtime across the business.
When It Makes Sense to Bring in Outside OT Security Support
Outside OT security support makes sense when the organization knows the risk is real but lacks the internal bandwidth, coordination, or visibility to move from concern to a managed program.
That often includes situations like these:
- Internal teams are already stretched across daily support and plant demands
- The environment includes aging systems and difficult vendor dependencies
- Security ownership is fragmented between operations, IT, and outside providers
- Leadership wants clearer governance and executive-ready reporting
- The business needs better monitoring, continuity planning, or managed security support
For manufacturers, outside support should add clarity and execution discipline, not more noise. The right partner helps the organization reduce risk in a way that respects plant realities, aligns stakeholders, and supports business continuity.
Building OT Security Around Uptime
OT security is operational resilience.
The practical path forward is to start with visibility, identify the assets that matter most to production, reduce unnecessary access, and build recovery readiness that reflects how the plant actually works. Manufacturers do not need abstract cybersecurity theory. They need a defensible program that protects uptime, supports safety, and reduces avoidable disruption.
The most effective improvements are usually the ones that bring stronger protection and clearer decision-making without adding unnecessary operational friction.
FAQs
What does it mean to secure OT and plant operations?
It means protecting the systems and connections that support production so the business can reduce cyber risk without compromising safety, uptime, or continuity.
What is the difference between OT security and IT security?
OT security focuses more heavily on availability, safety, and production continuity. Traditional IT security often places greater emphasis on confidentiality and standard device management.
Why are manufacturing plants frequent ransomware targets?
Because downtime is expensive, recovery is complex, and many environments have legacy systems, vendor access paths, and limited segmentation that make disruption more damaging.
Can you improve OT security without causing downtime?
Yes. A phased, risk-based approach can improve visibility, segmentation, access control, and recovery readiness while coordinating changes around maintenance windows and production schedules.
What is the first step in securing plant operations?
The first step is identifying critical OT assets and production dependencies so security priorities follow the systems and processes that matter most to operations.
How often should OT security risks be reviewed?
Risk reviews should happen regularly and also when production systems change, vendors change, new remote access paths are added, or incidents reveal new weaknesses.
When should a manufacturer bring in outside OT security expertise?
It makes sense when internal teams lack bandwidth, plant visibility is incomplete, responsibilities are fragmented, or leadership needs better governance, monitoring, and continuity planning.
Secure OT with clearer priorities and less disruption
If your team needs a practical plan to protect production without creating unnecessary downtime, talk with 7tech about securing OT without disrupting operations.

Neal Juern, CEO of 7tech, helps business leaders take control of their IT and strengthen cybersecurity without the complexity. Known for his straight-talk, business-first approach, Neal has guided hundreds of executives toward smarter, safer operations through Managed IT Services and Managed Security Services that make sense to people outside the IT department.