How to Protect Your Manufacturing Plant from Ransomware Without Slowing Production
To protect a manufacturing plant from ransomware without slowing production, focus on limiting how far an attack can spread and making recovery faster, cleaner, and more predictable. The goal is not perfect protection. It is reducing the chance that one compromised user, endpoint, or vendor connection can disrupt production across the plant.
For most manufacturers, the highest-value moves are straightforward: tighten identity controls, segment critical systems, govern vendor access, strengthen endpoint and application control, protect backups from production credentials, and rehearse isolation and recovery decisions before an incident happens.
TL;DR for executives
- Ransomware in manufacturing is a downtime problem first, not just a file-encryption problem.
- The biggest exposures are usually identity, remote access, flat networks, and weak recovery readiness.
- The most practical controls are MFA, least privilege, segmentation, backup protection, application control, vendor access discipline, and response planning.
- The objective is resilience without choking operations.
Why ransomware hits manufacturing differently
Ransomware is especially disruptive in manufacturing because the damage is measured in stopped production, missed schedules, shipment delays, and leadership pressure, not just inaccessible files. When plant operations depend on uptime, planning systems, remote support tools, shared storage, and connected users across multiple locations, a cyber event can quickly become an operations event.
That is why ransomware in manufacturing has to be managed as a continuity issue. Executives are not just asking whether data is encrypted. They are asking whether the plant can keep producing, whether orders can ship, whether quality processes can continue, and whether the business can recover in a controlled way.
This is also why broad prevention advice is not enough. Manufacturing environments need controls that protect availability and recovery without introducing unnecessary drag. That balance is reflected in NIST OT security guidance, which emphasizes security decisions that also respect safety, availability, and reliability.
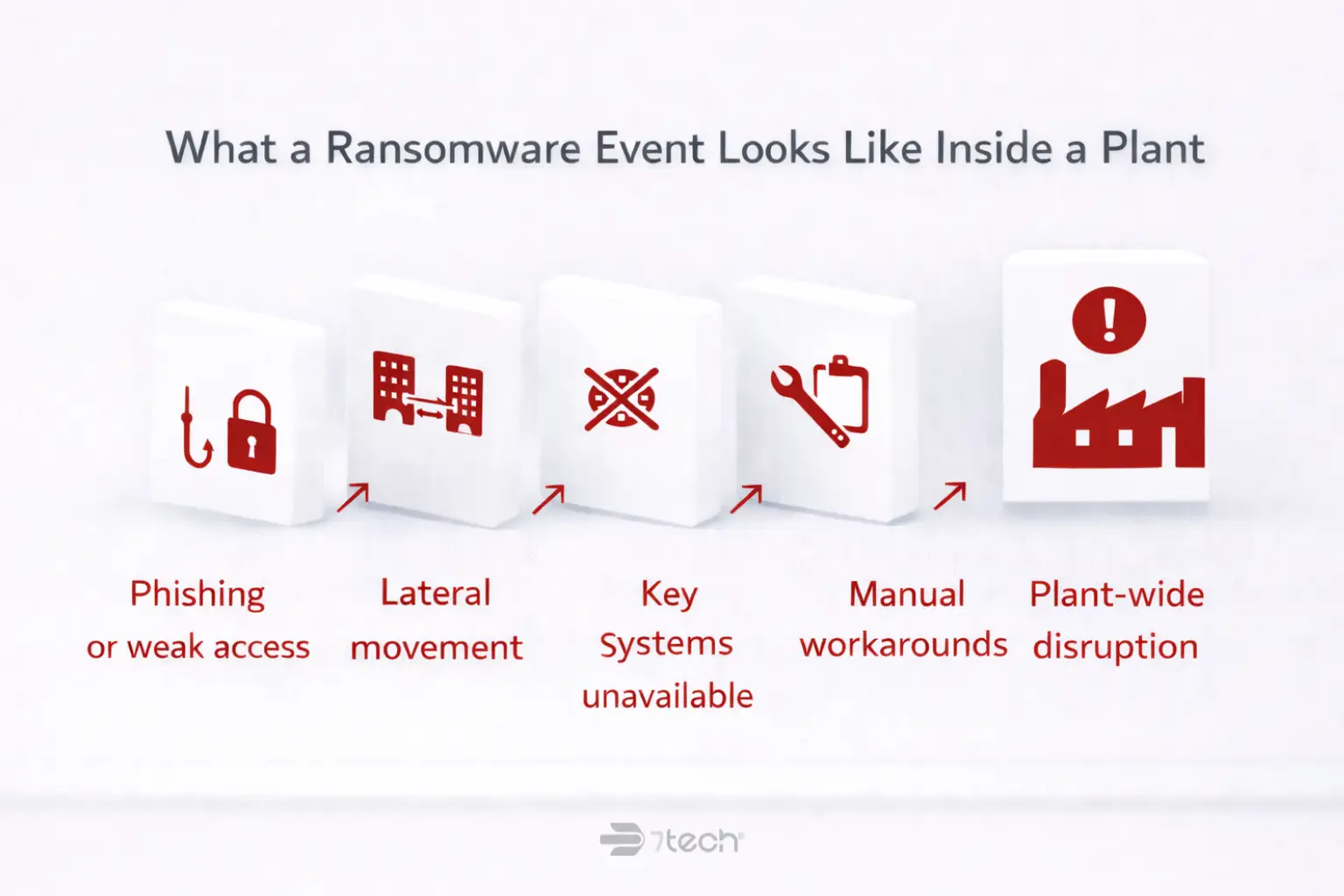
What a ransomware event looks like inside a plant
Most manufacturing ransomware events do not start with a dramatic plant-floor failure. They usually begin with something more ordinary: a phishing email, a reused password, a remote access tool left too open, or a vendor connection that has more access than it needs.
From there, an attacker may move laterally into systems that support scheduling, file access, production planning, remote sites, or administrative operations. Once key systems are unavailable, the business impact spreads quickly:
- Production scheduling becomes harder to trust or access
- ERP workflows slow down or stop
- Shared files and work instructions become unavailable
- Shipping and receiving coordination breaks down
- Vendor communication becomes fragmented
- Plant leadership and IT are forced into manual workarounds
The difference between a contained incident and a plant-wide outage often comes down to blast radius. That is why NIST manufacturing segmentation guidance is so relevant for manufacturers: it supports the practical idea that one compromised pathway should not lead to a plant-wide disruption.
Which systems create the biggest operational risk in a manufacturing plant
If you want to protect your manufacturing plant from ransomware, start with the systems that create the largest continuity exposure. Not every device has the same operational consequence. The right priority is business impact first.
Identity systems and privileged accounts
User accounts, admin credentials, and shared access often determine how quickly an attacker can move. If identity controls are weak, one compromised account can open the door to many systems at once.
ERP, file access, and production planning systems
These systems connect planning, scheduling, inventory, documentation, and execution. If they fail, the plant may still have equipment, labor, and demand, but not the coordination needed to ship reliably.
Remote access and third-party vendor connections
Manufacturers often depend on outside service providers, equipment vendors, and remote support teams. That makes vendor access security in manufacturing a business issue, not just a technical setting.
Shared networks between office and plant operations
When office users, plant support systems, remote tools, and sensitive operational dependencies share too much network trust, a small compromise can spread farther than leadership expects.
Backups and recovery dependencies
Backups only reduce ransomware downtime in manufacturing if they are protected, recoverable, and aligned to business restoration order. A backup that exists but cannot be restored cleanly under pressure is not much of a continuity plan.
How to protect your manufacturing plant from ransomware without slowing production
The most effective manufacturing ransomware protection strategy is usually phased, not disruptive. Start with the controls that reduce spread, reduce privilege, and improve recovery confidence.
1. Lock down identities before you buy more tools
Identity is one of the most common starting points for compromise, so begin there. Require MFA for privileged accounts, remote access, email, and any system that can open the door to broader access. Review privileged accounts, remove stale vendor access, and eliminate shared accounts wherever possible.
Also make offboarding discipline non-negotiable. Former staff, dormant contractors, and inherited admin accounts are common sources of avoidable risk. These are not glamorous fixes, but they are often the most immediate way to improve manufacturing ransomware prevention.
For broader context, 7tech’s guidance on practical ransomware prevention steps aligns with this same principle: get the basics of identity and access control right before assuming another product will solve the problem.
2. Segment the environment so one compromise does not become a plant-wide outage
Segmentation matters because it limits blast radius. Separate critical systems, user groups, and high-risk remote pathways so a compromise in one area does not automatically grant access to everything else.
This does not have to mean redesigning the whole plant. In many environments, the first win is simply reducing unnecessary east-west movement, tightening trust between office and operational dependencies, and isolating vendor pathways from general user access.
Executives do not need a deep OT architecture lesson here. They need a business rule: one compromised account or device should not be able to reach every important system.
If your organization is working toward a stronger access model, zero trust architecture is useful framing because it reinforces stricter access controls and fewer assumptions of trust inside the network.
3. Control applications and endpoints on the systems that matter most
Not every endpoint deserves the same level of control, but the systems that matter most to continuity should have tighter guardrails. Focus on approved application behavior, patch discipline, endpoint monitoring, and reduced unauthorized execution.
This is where many plant cybersecurity controls become practical rather than theoretical. The objective is not to burden production teams with complexity. It is to make high-consequence systems harder to misuse, harder to weaponize, and easier to monitor.
For many manufacturers, this is also the point where managed security services can help fill visibility and response gaps without forcing internal teams to build around-the-clock coverage on their own.
4. Tighten vendor and remote access before it becomes the weakest link
Manufacturing environments rely on external support more than many businesses realize. Equipment vendors, software providers, managed service partners, and maintenance teams often need remote access at the moments when production pressure is already high.
That is exactly why this access needs tighter discipline:
- Make access time-bound where possible
- Require MFA on remote tools
- Use approval workflows for elevated access
- Log vendor activity and review it
- Separate vendor access from standard user pathways
This is one of the clearest ways to improve security without slowing production. You are not removing support. You are making support more governable.
5. Build backups for recovery, not just compliance
Many leaders are told they have backups. The better question is whether those backups are protected from the same credentials and systems that could be compromised during an attack.
Strong recovery readiness usually includes protected backups, clear separation from production credentials, regular restore testing, and a documented recovery order by business priority. In a manufacturing setting, that means deciding what has to come back first for operations to resume in a controlled way.
That sequence should be driven by business dependency, not technical convenience. Manufacturers that want to reduce downtime should know which systems support shipping first, which systems support planning next, and which can wait.
If that visibility is unclear, a structured cybersecurity assessment checklist can help leadership identify the gaps before an incident forces the answer.
6. Prepare isolation and incident response before an event
A manufacturing incident response plan should answer practical questions in advance:
- Who has authority to isolate affected devices?
- Who owns communication between IT, plant leadership, and vendors?
- What gets shut down first if spread is suspected?
- When does the issue escalate from support problem to incident?
- How will decisions be documented for leadership and compliance needs?
The point is not to script every scenario. It is to remove hesitation at the worst possible moment. CISA’s CISA ransomware guidance is useful here because it reinforces the same business reality: ransomware readiness is about prevention, containment, and recovery planning together.
What good recovery readiness looks like before an incident
Good recovery readiness is visible before anything goes wrong. Leadership should be able to answer five questions clearly:
| Recovery question | What good looks like |
|---|---|
| What matters most? | Critical systems are prioritized by operational impact, not by technical preference. |
| Who owns each system? | Every critical platform has a business owner and a technical owner. |
| Can we restore it? | Restore procedures are documented and tested, not assumed. |
| How fast can it return? | Downtime expectations are realistic and communicated in advance. |
| What if restoration is partial? | Leadership knows what can resume first and what dependencies remain blocked. |
This is where manufacturing backup and disaster recovery becomes an executive topic. If leaders do not know what can be restored quickly, they cannot make calm decisions under pressure.
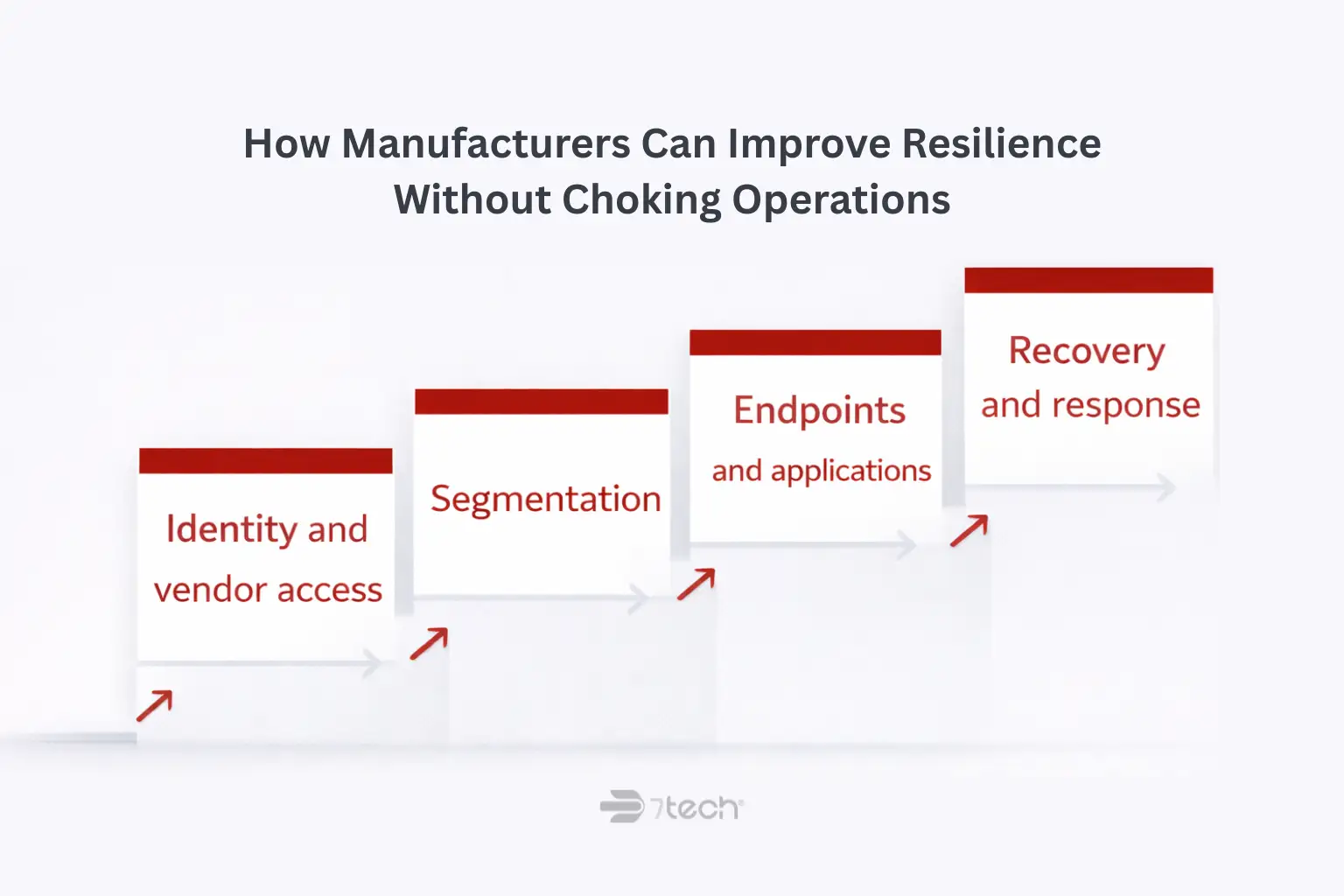
How manufacturers can improve resilience without choking operations
The practical path is phased improvement. Start with the systems whose failure would stop shipping, disrupt planning, or create the greatest leadership exposure. Then sequence controls by risk reduction and operational impact.
That often means addressing identity and vendor access first, then segmenting the most consequential pathways, then tightening endpoint and application behavior on high-value systems, then strengthening recovery testing and response discipline.
This is also why manufacturing IT services and security planning should be aligned to plant continuity, not treated as separate conversations. The best manufacturing cybersecurity best practices are the ones the business can actually sustain.
Manufacturers looking for a broader strategy view may also benefit from 7tech’s perspective on manufacturing security strategies, especially when leadership wants to connect ransomware resilience to the larger security posture without turning the discussion into a major redesign project.
Questions leaders should ask if they want to protect a manufacturing plant from ransomware
- If one user account were compromised, how far could an attacker move?
- Which systems would stop shipping first?
- Could we isolate affected systems quickly without waiting for debate?
- Have we tested backup restoration for the systems that matter most to operations?
- How much vendor access do we currently allow, and who reviews it?
- Are office and plant dependencies separated enough to limit spread?
- Do leadership, IT, and plant operations agree on recovery order?
When to get outside help
Outside help makes sense when internal IT is stretched, when vendor sprawl makes ownership unclear, or when leadership does not have confidence in segmentation, recovery testing, or monitoring coverage. That does not mean internal teams are failing. It means the environment has become too important and too interconnected to manage reactively.
For manufacturers, the real issue is often visibility. If leadership cannot clearly explain where the largest ransomware exposure lives, what would stop production first, or how the business would recover in order, outside guidance can help turn a vague concern into a defensible plan.
“Since working with them, everything feels more competent and our day-to-day workflow runs smoother and more reliably. They also bring in modern technology that actually supports our operation instead of holding it back.”
— Hugh Goldberg, Supply Chain Director, Prytime Medical Devices
FAQ
How do you protect a manufacturing plant from ransomware?
Start by reducing blast radius and improving recovery. The most practical controls are MFA, least privilege, segmentation, vendor access discipline, endpoint and application control, protected backups, and a tested incident response plan.
Why is ransomware especially disruptive in manufacturing?
Because the impact is operational. A ransomware event can interrupt scheduling, ERP access, shared documentation, shipping coordination, and plant workflows, which makes downtime the primary business risk.
What controls matter most for preventing plant-wide spread?
Identity control, network segmentation, remote access discipline, and tighter vendor access usually matter most. These reduce the chance that one compromised user, device, or connection can reach critical systems across the plant.
Can you improve ransomware protection without disrupting production?
Yes. Most manufacturers can improve resilience through phased controls that target the highest-consequence systems first, instead of trying to redesign the entire environment at once.
What should manufacturers test before a ransomware incident?
They should test backup restoration, isolation decisions, escalation paths, communication workflows, and recovery order for critical systems. The key question is not whether a backup exists, but whether recovery works under pressure.
Get a clearer view of plant ransomware exposure
If you want a calmer, more practical view of where ransomware risk could disrupt production, 7tech’s Manufacturing Operational Scorecard is a useful next step. It is designed to help leadership see operational exposure, recovery readiness, and control gaps more clearly without turning the conversation into a pressure-driven sales process.
Call (844) 701-6777 to request the Manufacturing Operational Scorecard.

Neal Juern, CEO of 7tech, helps business leaders take control of their IT and strengthen cybersecurity without the complexity. Known for his straight-talk, business-first approach, Neal has guided hundreds of executives toward smarter, safer operations through Managed IT Services and Managed Security Services that make sense to people outside the IT department.